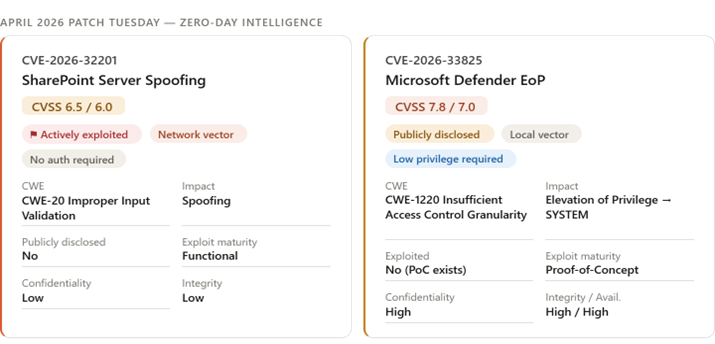
April 2026 is the second-largest Microsoft Patch Tuesday on record (247 total CVEs). ZDI and Rapid7 analysts attribute the surge, particularly the ~60 browser vulnerabilities included via Chromium, to AI-assisted vulnerability discovery. The Patch Tuesday addressed two significant 0-day vulnerabilities. CVE-2026-32201 is a SharePoint Spoofing vulnerability that has been actively exploited in the wild. CVE-2026-33825 is an Elevation of Privilege (EoP) vulnerability in Microsoft Defender that was publicly disclosed prior to a fix being available.
Severity: Critical
Vulnerability Overview
1. CVE-2026-32201 – SharePoint Spoofing
- This is the higher operational priority despite its lower CVSS score (6.5).
- The root cause is improper input validation (CWE-20) in SharePoint’s network-facing layer, requiring zero authentication and zero user interaction, making it trivially scalable.
- The post-exploitation impact is limited to data view/modification (no availability impact), suggesting it is likely being used for credential theft, session hijacking, or reconnaissance rather than destructive attacks.
- Affected Products: SharePoint Server Subscription Edition, 2019, and 2016.
2. CVE-2026-33825 — Microsoft Defender EoP
- A proof-of-concept is publicly available, and the vulnerability is rated “Exploitation More Likely” by Microsoft.
- It is a local privilege escalation to SYSTEM via insufficient access control granularity in the Defender platform meaning an attacker who has already gained a foothold (perhaps via the SharePoint flaw) could chain this to fully compromise the host.
- This chaining scenario makes the two vulnerabilities particularly dangerous together. Remediation is largely automatic if Defender’s update mechanism is working, but fleet-wide verification is essential.
- Affected Products: Microsoft Defender Antimalware Platform versions prior to 4.18.26030.3011.
Other Notable Microsoft Cves
1. CVE-2026-33827 (Wormable candidate, CVSS 8.1, Windows TCP/IP remote code execution)
Remote, unauthenticated RCE with no user interaction potentially wormable on systems with IPv6 + IPSec enabled. Race condition limits reliability but ZDI notes race conditions are routinely exploited at Pwn2Own. Patch before public exploits emerge.
2. CVE-2026-33824 (Wormable candidate, CVSS 9.8, Windows IKE service extensions RCE)
Second wormable-class bug this month. Affects systems with IKE enabled. External attack blocked by filtering UDP 500/4500 at the perimeter, but insider lateral movement remains possible. Enterprises using IKE should prioritise.
3. CVE-2026-26149 (Security bypass, CVSS 9.0, Microsoft Power Apps security feature bypass)
Allows attackers to bypass a security warning and trick users into triggering external protocol calls that perform unintended device actions. Social engineering + protocol abuse vector.
4. CVE-2026-23670 (Virtualization-Based Security (VBS) bypass, CVSS 5.7)
Allows a compromised Windows kernel (VTL0) to manipulate memory in the secure kernel (VTL1) — breaking VBS isolation guarantees. ZDI calls this the most interesting security-bypass of the month. Undermines hardware-backed security assumptions.
Recommendations
- Prioritise SharePoint patching immediately. Apply the relevant KB for your SharePoint version (SE: 5002853, 2019: 5002854, 2016: 5002861). If patching is delayed, restrict external network access to SharePoint and enable enhanced logging on SharePoint ULS and WAF for spoofing indicators.
- Microsoft Defender typically auto-updates. Confirm all endpoints are running Antimalware Platform ≥ v4.18.26030.3011.
- Test and deploy TCP/IP and IKE patches urgently. Interim: block UDP 500/4500 at the perimeter for IKE. Monitor for public exploit code, which has not yet appeared but is likely to emerge given the wormable class.
- Users should update their Chromium-based browsers to the latest version.
Source:
- https://msrc.microsoft.com/update-guide/en-US/advisory/CVE-2026-32201
- https://msrc.microsoft.com/update-guide/en-US/advisory/CVE-2026-33825
- https://www.zerodayinitiative.com/blog/2026/4/14/the-april-2026-security-update-review
- https://krebsonsecurity.com/2026/04/patch-tuesday-april-2026-edition/
Enjoyed reading this Threat Intelligence Advisory? Stay updated with our latest exclusive content by following us on Twitter and LinkedIn
No related posts found.