Most cyberattacks don’t announce themselves. They move quietly through compromised credentials, unusual login patterns, slow data transfers until the damage is done. Security monitoring is what stands between early detection and a full-scale breach. In this blog, we answer the key questions every organization should be asking about how security monitoring works, what it covers, and why it matters.
At 2:13 AM, an employee account logs in from Bengaluru. Three minutes later, the same credentials attempt access from another country. Moments after that, sensitive files begin moving to an unknown external destination. No one inside the company notices anything unusual. Operations continue to be normal.
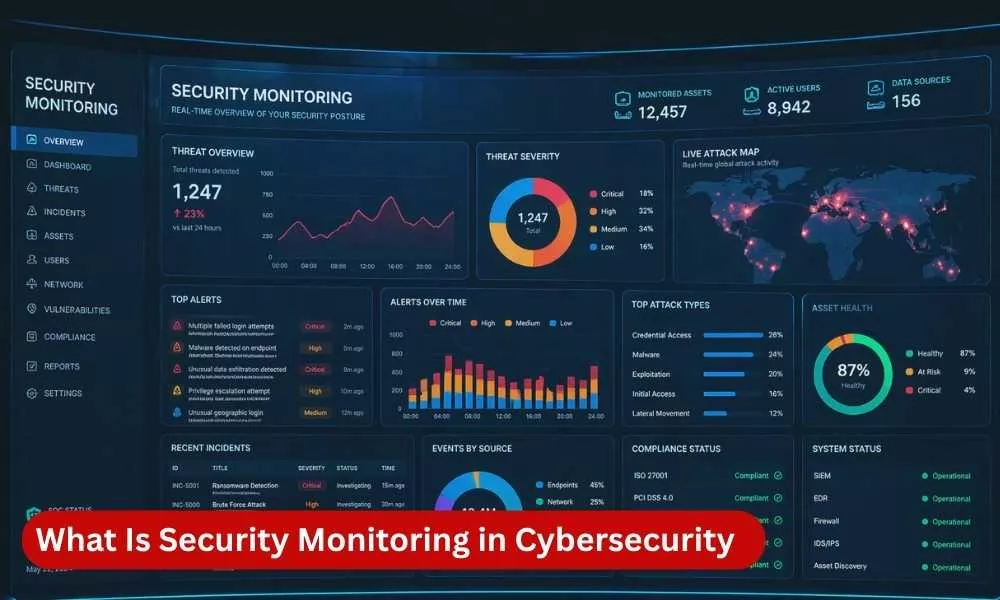
But the organization’s Security Operations Center (SOC) does. Security monitoring tools detect impossible travel activity, suspicious login behavior, privilege misuse, and abnormal data transfer patterns in real time. The alert escalates immediately. Analysts isolate the compromised account, block access, and stop a potential breach before business hours begin.
This is how modern security monitoring works. It transforms thousands of daily logs, events, and user activities into actionable intelligence, helping organizations detect and respond to threats before serious damage occurs.
What is Security Monitoring?
Security monitoring in cybersecurity is the continuous process of collecting, analyzing, and reviewing digital activity across systems, networks, applications, and users to detect potential threats, policy violations, and suspicious behavior. It provides ongoing visibility into an organization’s IT environment so that security incidents can be identified and addressed before they escalate into breaches, data loss, or operational disruption.
Unlike one-time security assessments or periodic audits, security monitoring operates continuously. It focuses on identifying abnormal behavior, indicators of compromise, unauthorized access attempts, and misconfigurations in real time or near real time.
At its core, security monitoring answers one critical question: What is happening inside our environment right now? In this blog we will explore almost everything about security monitoring across cybersecurity.
Why Do You Need a SOC?
Security monitoring is essential for organizations that handle sensitive data, operate cloud or hybrid environments, process financial transactions, support remote workforces, or meet regulatory obligations. A Security Operations Center (SOC) strengthens this capability by providing continuous threat detection, faster incident response, and expert oversight. Organizations rely on SOC teams to reduce ransomware, phishing, insider threats, and unauthorized access risks while maintaining business continuity. Many compliance frameworks such as ISO 27001, PCI DSS 4.0, SOC 2, HIPAA, and NIST require or strongly expect monitoring, logging, and incident response controls. In practice, nearly all modern organizations benefit from SOC-led continuous security monitoring.
What Does Security Monitoring Actually Monitor?
Security monitoring covers multiple layers of an organization’s digital environment. It includes the following:
- Network traffic: inbound and outbound communication patterns.
- Endpoints: laptops, servers, mobile devices, and workstations.
- Applications: web applications, SaaS platforms, APIs.
- Cloud infrastructure: virtual machines, storage, containers.
- Identity and access systems: login activity, privilege changes.
- Security devices: firewalls, intrusion detection systems, gateways.
Each of these layers generates logs and events that are collected and analyzed for signs of abnormal activity.
How Does Security Monitoring Work?
Security monitoring follows a structured lifecycle consisting of data collection, analysis, detection, and response.
1. Data Collection
Systems and devices generate logs that record events such as login attempts, file access, configuration changes, and network connections. These logs are gathered from multiple sources and forwarded to centralized platforms.
2. Log Aggregation and Correlation
Logs are consolidated into a centralized system such as SIEM (Security Information and Event Management) platform, a software solution designed to enhance defensive posture by collecting and analyzing data from various sources across an IT environment. It provides a centralized platform for monitoring, detecting, and responding to potential security threats in real time. Popular examples include Splunk and IBM QRadar. These platforms correlate events from different sources to identify patterns that may indicate malicious behavior.
3. Threat Detection
Detection mechanisms analyze events using predefined correlation rules, behavioral analytics, anomaly detection, threat intelligence feeds, and machine learning models. The goal is to identify suspicious activity that deviates from normal behavior.
4. Alerting and Investigation
When a potential threat is identified, alerts are generated. Security analysts review these alerts to determine whether they represent a true incident or a false positive.
5. Incident Response
If confirmed, the organization initiates containment, remediation, and recovery actions to limit damage.
What Tools Are Used in Security Monitoring?
Security monitoring relies on multiple technologies that work together. This includes:
- SIEM (Security Information and Event Management): Centralizes logs from multiple sources and correlates events to detect threats.
- SOAR (Security Orchestration, Automation, and Response): Automates security workflows, investigations, and incident response across integrated tools.
- EDR (Endpoint Detection and Response): Detects, investigates, and responds to malicious activity on endpoint devices.
- NDR (Network Detection and Response): Monitors network traffic to identify anomalies, lateral movement, and hidden threats.
- XDR (Extended Detection and Response): Unifies security data across endpoints, networks, cloud, and email for faster threat detection and response.
Each tool addresses a different layer of visibility, but effective monitoring requires integration across them.
What Is a SOC in Security Monitoring?
A Security Operations Center (SOC) is a centralized team responsible for continuously monitoring, detecting, analyzing, and responding to cybersecurity incidents.
A SOC typically operates 24/7 and performs functions such as alert triage, incident investigation, threat hunting, vulnerability tracking, and reporting and compliance support Security monitoring technology without skilled analysts can generate alerts, but interpretation and decision-making require human expertise.
What Types of Threats Can Security Monitoring Detect?
Effective security monitoring can detect unauthorized access attempts, privilege escalation, malware infections, ransomware activity, suspicious login behavior, data exfiltration attempts, lateral movement within networks, and configuration changes that weaken security. The effectiveness of detection depends on rule quality, system integration, and continuous tuning.
What Is the Difference Between Security Monitoring and Threat Detection?
Security monitoring is the broader, continuous process of observing systems and collecting data. Threat detection is a component within monitoring that identifies malicious or suspicious activity within that data. Monitoring provides visibility.
Detection identifies risk within that visibility.
How Does Security Monitoring Support Compliance?
Many regulatory and governance frameworks require continuous monitoring as part of risk management and control effectiveness. For example, standards from the International Organization for Standardization and guidance from the National Institute of Standards and Technology emphasize ongoing log review, incident detection, and response capabilities.
Security monitoring helps organizations demonstrate continuous oversight, provide audit evidence, detect policy violations, & maintain control effectiveness. It transforms compliance from periodic documentation into operational oversight.
What Are the Challenges of Security Monitoring?
Although critical, security monitoring presents operational challenges such as high alert volumes leading to analyst fatigue, false positives that consume investigation time, complex log integration across hybrid environments, high storage and processing costs, and skill shortages in cybersecurity operations.
To address these challenges, organizations must continuously tune detection rules, refine alert thresholds, and automate repetitive tasks.
Who Needs Security Monitoring?
Security monitoring is essential for any organization that handles sensitive data, operates cloud or hybrid environments, processes financial transactions, supports remote workforces, and is subject to regulatory compliance.
In practice, nearly all modern organizations require some form of continuous security monitoring.
Final Summary
Security monitoring in cybersecurity is the continuous process of collecting, analyzing, and responding to security-related events across digital environments.
It combines technology, processes, and skilled analysts to detect threats, reduce dwell time, and maintain operational resilience. By providing real-time visibility into system activity, security monitoring enables organizations to move from reactive incident handling to proactive threat management.
In a connected and dynamic threat arena, security monitoring is not optional. It is a foundational capability for protecting digital assets and maintaining trust.
| Learn how continuous monitoring enables faster detection and smarter response. Connect with our security monitoring experts today! |
Enjoyed reading this blog? Stay updated with our latest exclusive content by following us on Twitter and LinkedIn.