Quantum computing is rapidly reshaping the future of cybersecurity, making traditional encryption methods increasingly vulnerable to the “harvest now, decrypt later” threat model. This blog explores why organizations need both crypto-agility and post-quantum cryptography (PQC) to achieve true quantum resilience. While crypto-agility enables enterprises to quickly adapt and replace cryptographic algorithms, PQC delivers the quantum-resistant protection needed to secure sensitive data against future quantum attacks. Together, they form the foundation of a scalable, NIST-aligned quantum security strategy for modern enterprises.
Five years from now, the breach notification will not come from a firewall alert or a SIEM dashboard. It will come from a regulator. Specifically, from an investigator who had spent three weeks tracing a cache of intercepted ciphertext, harvested in 2024 from a mid-sized financial services firm, that had just been decrypted, completely and cleanly, without a single login, phishing email, or zero-day exploit. The firm’s encryption had been unimpeachable by 2024 standards. It was RSA-2048. The quantum computer that broke it didn’t care.
The CISO remembered the board meeting where quantum risk had been moved to “the long-term roadmap.” The legal team was already on the phone. The data having eight years of customer transaction records was now readable by whoever had the patience to wait.
This scenario is not speculative fiction. It is the documented logic of the harvest now, decrypt later threat model. And it is why the conversation about crypto-agility and post-quantum cryptography cannot wait for quantum computers to arrive.
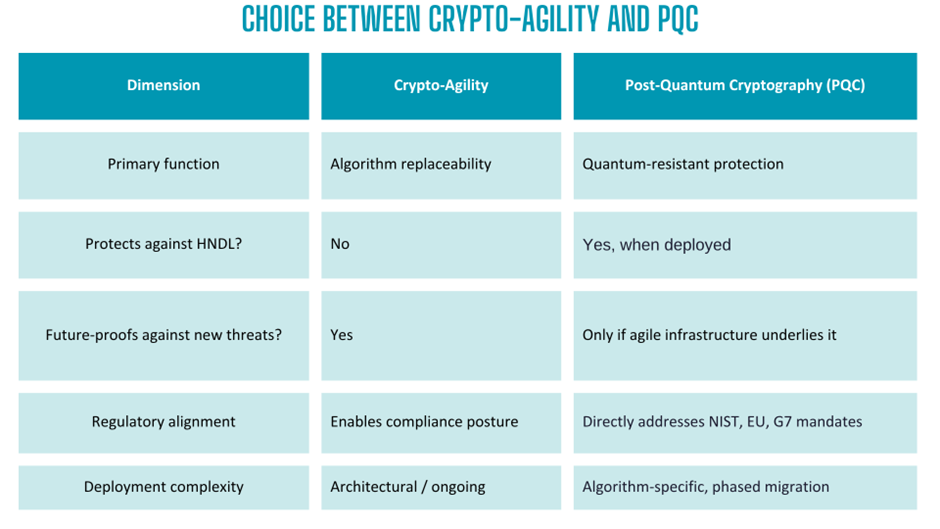
Most enterprise security teams are now aware of the quantum threat. What they often miss is that deploying post-quantum cryptography (PQC) algorithms is only half the answer, and that crypto-agility, while a critical enabler, is not a destination. The organizations that will weather the quantum transition are those that understand precisely where each capability begins and ends.
The Quantum Threat Future is Here!
Quantum computing is advancing fast enough that the cryptographic foundations of today’s enterprise infrastructure including RSA, elliptic-curve cryptography (ECC), and Diffie-Hellman for key exchange, face real obsolescence within the decade. In August 2024, the National Institute of Standards and Technology (NIST) finalized its first set of post-quantum cryptography standards (FIPS 203, 204, and 205), marking the transition from theoretical preparation to active regulatory urgency.
More immediately alarming is the “harvest now, decrypt later” (HNDL) threat model. Adversaries are already exfiltrating encrypted data today; financial records, health data, classified communications, intellectual property, with the intent to decrypt it the moment a cryptographically relevant quantum computer (CRQC) becomes available. That moment could be 2030or even sooner. The data they harvest today has a lifespan that may far outlast your current encryption.
Note for the Healthcare & HIPAA Teams
Protected health information (PHI) carries some of the longest data retention lifespans in any regulated industry; patient records are often stored for decades. Under the HNDL threat model, that makes healthcare one of the highest-risk verticals of all. Data being transmitted today across payer networks, EHR systems, and telehealth platforms is a prime harvesting target. Organizations subject to HIPAA and HITRUST obligations should treat PHI encryption as their first PQC migration priority, not a future compliance footnote.
This means the quantum migration window is not a future deadline. It is already open, and enterprises that defer action are compounding their exposure with every passing quarter.
What Crypto-Agility Means and Where It Stops?
Crypto-agility refers to an organization’s architectural ability to swap out cryptographic algorithms, key types, and protocols efficiently, without redesigning every system from scratch. It is fundamentally a property of how cryptography is implemented, not which cryptography is in use at any given moment.
A crypto-agile enterprise has completed a cryptographic inventory, understands where each algorithm is deployed across its stack, cloud workloads, hardware security modules (HSMs), APIs, TLS configurations, mobile applications, IoT devices and has abstracted its crypto dependencies so that swapping ML-KEM for RSA is a configuration change, not a re-architecture project.
This is indispensable as without crypto-agility; even a perfectly chosen PQC algorithm becomes a liability when it is eventually superseded, weakened, or deprecated, which history tells us is inevitable. No algorithm lasts forever. Crypto-agility is the infrastructure that makes quantum migration manageable. But it doesn’t make your data quantum-resistant today.
The critical limitation: crypto-agility is a capability of posture, not a protection mechanism. An agile system that is still running RSA-2048 remains fully vulnerable to a Cryptographically Relevant Quantum Computer (CRQC). Agility tells you how fast you can change. It says nothing about whether you are currently protected. This is where PQC enters and where the confusion between the two concepts causes real strategic damage.
What Post-Quantum Cryptography Delivers and Its Own Blind Spots
Post-quantum cryptography addresses the protection gap directly. NIST-standardized algorithms including ML-KEM (formerly CRYSTALS-Kyber) for key encapsulation, ML-DSA and SLH-DSA for digital signatures, are designed to withstand attacks from both classical and quantum computers. Deploying these algorithms replaces the mathematical problems (large integer factorization, discrete logarithms) that quantum hardware can solve efficiently.
PQC also addresses the HNDL threat in a way crypto-agility alone never can: only by migrating to quantum-resistant algorithms now can an organization protect data in transit from adversarial collection that targets future decryption.
However, PQC migration without crypto-agility creates a different class of risk. PQC algorithms are comparatively new. They have not endured the decades of real-world cryptanalysis that RSA and ECC have. NIST’s own process acknowledges this uncertainty, which is why it selected HQC as a backup key encapsulation algorithm in March 2025. Enterprises that have hard-code PQC implementations without agile infrastructure are essentially making the same architectural mistake twice: building systems that cannot adapt when the threat landscape evolves again.
For a deeper look at how PQC and crypto-agility interact at a global infrastructure level, the GSMA’s technical analysis illustrates why mobile and enterprise networks must address both dimensions simultaneously.
Why Enterprises Need Both: The Case for a Unified Cryptographic Strategy
The false choice between crypto-agility and PQC dissolves when viewed through a risk management lens. They operate at different layers of the security stack and solve distinct, but deeply complementary, problems.
Board & Audit Committee Briefing, Translating Quantum Risk
For CFOs and audit committee members, the quantum risk is not theoretical. It carries measurable financial exposure: The IBM Cost of a Data Breach Report 2025 shows the global average fell 9% to $4.44 million, down from $4.88 million in 2024. Regulatory fines under GDPR, HIPAA, and PCI DSS for failures to implement adequate encryption controls regularly compound that exposure further. A successful HNDL attack on encrypted financial records or PHI could trigger liability years after the initial exfiltration, long after legacy encryption has been retired.
The business case for quantum readiness is not “spend now on an uncertain future threat.” It is “the data being transmitted today may become a regulatory and reputational liability within five years, and the cost of proactive migration is a fraction of the cost of breach response, litigation, and regulatory remediation.”
The recommended approach across industry guidance from financial sector roadmaps to critical infrastructure frameworks is the hybrid model: run PQC algorithms alongside existing classical algorithms during the transition period. This provides immediate quantum-resistant protection while allowing operational continuity and backward compatibility. Crypto-agility is what makes this hybrid approach feasible to manage at enterprise scale.
Ampcus Cyber’s Security Architecture Review methodology specifically evaluates how current cryptographic dependencies are embedded in your architecture and whether your systems have the agility to support a phased PQC migration. This is a foundational step before any algorithm selection or vendor engagement.
From Cryptographic Inventory to Quantum Resilience
The path from awareness to quantum resilience follows a repeatable sequence, regardless of industry or infrastructure complexity.
- Discover and inventory: Map every location where public-key cryptography is in use such as TLS endpoints, code-signing pipelines, HSMs, key management systems, legacy applications, third-party APIs, and IoT and OT devices. Operational technology environments are especially high-risk: firmware update cycles are long, patching windows are narrow, and embedded cryptographic libraries are rarely abstracted. Most organizations underestimate this footprint by a significant margin.
- Prioritize data lifetime and exposure: Long-lived data, high-value credentials, and externally transmitted records are HNDL-vulnerable today. Healthcare PHI, financial records, and classified communications require accelerated migration timelines.
- Establish cryptographic agility as infrastructure including in your dev pipeline: Abstract crypto dependencies at the library and configuration layer. For DevSecOps teams, this means selecting TLS and signing libraries that support algorithm negotiation, ensuring CI/CD pipelines enforce quantum-safe code-signing standards, and avoiding hard-coded algorithm references in application code. Centralized key management should support algorithm transitions without requiring application rebuilds.
- Deploy hybrid PQC for highest-risk data flows: Begin with NIST-standardized algorithms (ML-KEM, ML-DSA) on critical data channels. Run in hybrid mode alongside classical algorithms during the validation period.
- Align to regulatory timelines including CMMC for defense contractors: The EU has set end-2026 as a transition milestone, with end-2030 as the critical infrastructure deadline. Defense contractors operating under CMMC and NSA CNSA 2.0 guidelines face some of the strictest and earliest PQC adoption deadlines of any sector. Financial services firms and government contractors should treat their compliance calendar as the migration forcing function.
Executing this roadmap requires a structured risk assessment framework that can quantify cryptographic exposure in business terms, not just technical ones. CISOs need to present quantum risk to boards and audit committees in the same language as any other material operational risk.
Aligning this work to established frameworks such as the NIST Cybersecurity Framework ensures that cryptographic modernization integrates into your broader governance posture rather than running as an isolated workstream. Organizations without dedicated security leadership may also benefit from engaging Virtual CISO (vCISO) to drive the PQC migration strategy without the overhead of a full-time hire. Mid-market organizations that lack an existing cryptographic inventory should not view this as a barrier to entry; the inventory itself is the starting point, and a structured assessment can establish your baseline in weeks, not quarters.
Building internal PQC capability matters too. As quantum-resistant cryptography becomes a baseline compliance expectation, the demand for teams that understand it will outpace supply. Ampcus Cyber’s practitioner certifications including CAISS (Certified AI Security Specialist) and CARTP (Certified AI Red Team Professional) are designed to build the hands-on skills needed to implement, audit, and stress-test PQC deployments in real-world environments. Upskilling your security team now reduces long-term dependency on external expertise and accelerates every stage of the migration roadmap.
The bottom line for enterprise security leaders is this: crypto-agility without PQC leaves you exposed to a threat that is actively exploiting your data today. PQC without crypto-agility leaves you rigidly dependent on algorithms that will eventually need replacement. The quantum-resilient enterprise needs both implemented in sequence, governed as a continuous program, and aligned to regulatory and threat of intelligence timelines.
Is Your Cryptographic Infrastructure Quantum Ready?
Ampcus Cyber helps security teams of every size build the crypto-agility foundation, execute NIST-aligned PQC migration roadmaps, and quantify quantum risk before it becomes a board-level incident. Choose the path that fits where you are today.
| Speak with an Ampcus Cyber expert and learn about your organization’s post-quantum cryptography exposure today. |
Enjoyed reading this blog? Stay updated with our latest exclusive content by following us on Twitter and LinkedIn.