“Move beyond checklists. See how compliance risk can be quantified in financial terms and translated into continuous, real-time visibility.”
For years, governance, risk, and compliance programs have operated on a foundation of qualitative judgment. Risk registers populated with High / Medium / Low ratings, compliance status tracked through static spreadsheets, and audit readiness measured by the stack of evidence folders assembled weeks before an assessment, these are the hallmarks of a GRC approach that was never designed for the speed, volume, or interconnectedness of modern enterprise risk.
The consequences of this gap are well-documented. According to the IBM Cost of a Data Breach Report 2024, organizations with low levels of security posture maturity, a direct proxy for weak GRC practices, experienced breach costs averaging USD 5.17 million, nearly 30% higher than organizations with mature, continuously monitored compliance programs.
Yet most enterprises still struggle to translate compliance gaps and control weaknesses into quantified financial exposure. The question “how much risk do we actually carry?” remains unanswered in boardrooms worldwide.
From Static Compliance to Continuous Risk Visibility
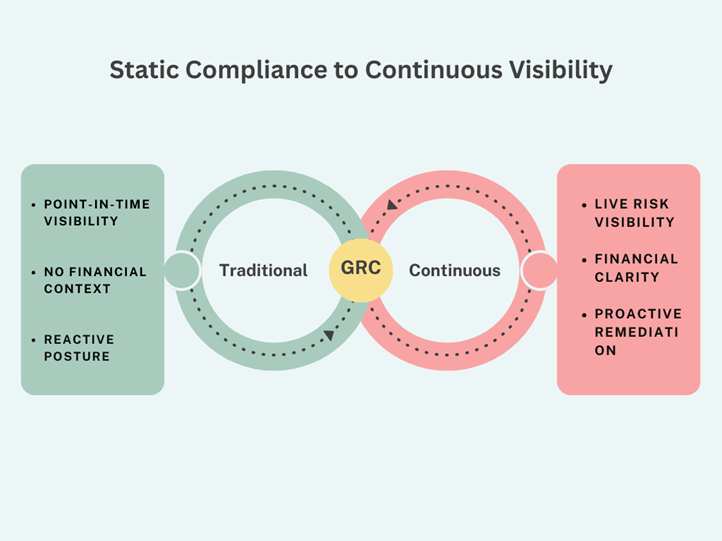
This shift reflects a broader transition from compliance as documentation to compliance as a continuously measurable risk discipline.
What Cyber Risk Quantification Means
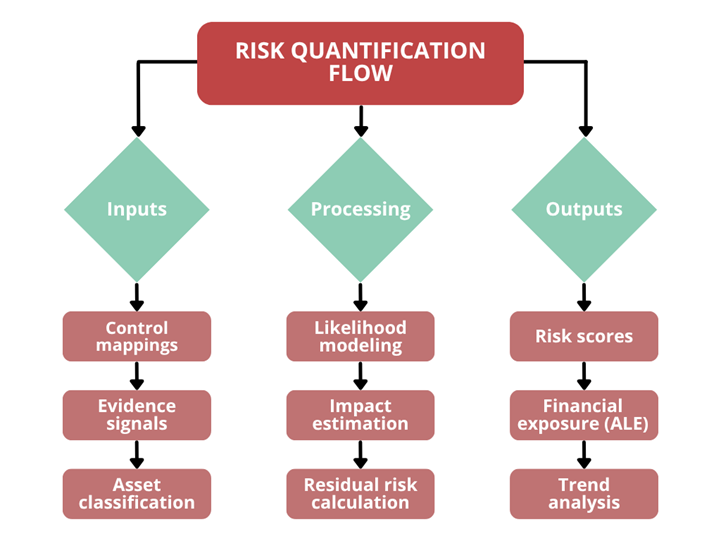
Risk quantification is the process of assigning measurable, defensible values to compliance gaps, control failures, and audit findings, expressing them not merely as ordinal severity ratings but as estimated financial exposure, likelihood-weighted impact, and residual risk scores that can be tracked over time and reported to executive stakeholders.
The Three Capabilities Behind Risk Quantification
Effective risk quantification depends on three interlocking mechanisms: cross-framework control mapping, continuous evidence monitoring, and automated risk scoring. These mechanisms feed into a unified risk model that maintains a dynamic view of organizational risk as compliance posture shifts.
Cross-Framework Control Mapping as a Risk Signal
Compliance obligations span multiple frameworks, PCI DSS, ISO 27001, NIST CSF, HIPAA, SOC 2, HITRUST, CMMC, and others. When a single control gap maps to multiple frameworks simultaneously, the associated risk increases proportionally, reflecting compounded regulatory exposure.
A missing access review, for instance, may constitute a finding under PCI DSS Requirement 7, ISO 27001 Annex A 9.2, and SOC 2 CC6.1 concurrently, a risk that a siloed approach would count once, but which in reality represents a multi-framework exposure.
Continuous Evidence Monitoring as a Risk Pulse
Traditional compliance programs treat evidence collection as a periodic activity. Continuous models invert this approach by maintaining an ongoing evidence pipeline that monitors control effectiveness in real time.
When evidence degrades a policy document goes stale, a vulnerability scan fails threshold, or an access review lapses risk increases immediately.
This temporal dimension is critical. It captures the difference between controls that exist on paper and controls that are operationally effective a distinction that point-in-time audits routinely miss.
Automated Risk Scoring and Residual Risk Tracking
Risk scoring models combine inherent risk weighting derived from asset criticality, regulatory classification, and data sensitivity with control effectiveness signals derived from continuous monitoring.
Translating Compliance Gaps into Financial Exposure
One of the most significant capabilities in modern GRC is the ability to express compliance gaps in financial terms, bridging the communication divide between technical teams and executive stakeholders.
Approaches such as Factor Analysis of Information Risk (FAIR) map control gaps to probable loss event frequencies and loss magnitudes using industry benchmark data.
A critical finding in access management, for example, can be associated with a probability distribution of breach scenarios, producing an annualized loss expectancy (ALE) estimate that can be presented as a defensible financial figure rather than a subjective severity label.
From Annual Audit Panic to Year-Round Assurance
Conventional GRC tools are architected around the audit cycle. The distinction between audit-centric and continuous models is consequential.
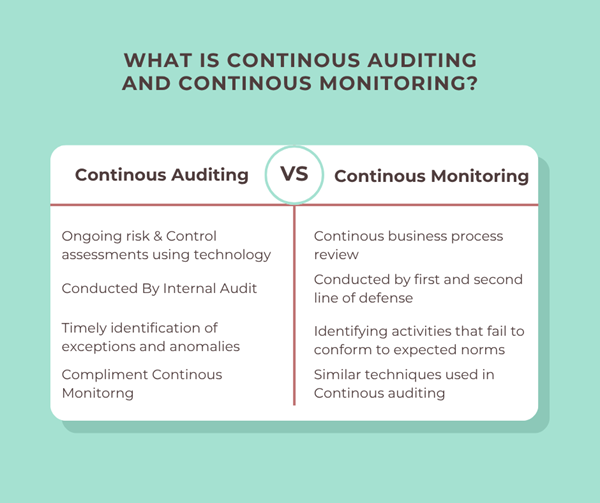
In a continuous model, audit readiness becomes a by-product of operational discipline rather than a periodic sprint. Risk data remains current, and reporting reflects the organization’s actual control effectiveness at any given moment.
Third-Party Risk as Part of the Same Equation
Enterprise risk does not stop at the organizational boundary. Vendors, cloud providers, and supply chain partners contribute directly to compliance exposure.
Modern approaches integrate third-party risk into the same risk model, applying control effectiveness scoring and financial exposure modeling across both internal and external environments.
This unified view is essential for accurately understanding total organizational risk, particularly under regulatory frameworks that extend accountability to service providers.
Risk Reporting That Speaks to the Board
Risk quantification has limited value if its outputs remain confined to GRC dashboards. Executive stakeholders require risk to be expressed in financial and strategic terms.
Board-level reporting increasingly focuses on:
- Financial exposure ranges
- Risk trends over time
- Return on control investment
This represents a shift from compliance reporting as a checklist to risk reporting as a decision-making tool.
Where ComplyX GRACE Fits
Platforms like ComplyX GRACE operationalize these capabilities by embedding risk quantification into continuous compliance workflows.
GRACE enables:
- Cross-framework control normalization
- Continuous evidence monitoring
- Automated, dynamic risk scoring
- Financial risk translation using established models
- Unified visibility across internal and third-party risk
Rather than functioning as a post-hoc reporting layer, it maintains a real-time, continuously updated risk register aligned with the organization’s evolving compliance posture.
Conclusion: Risk Quantification as a Strategic Discipline
Compliance has never been solely about satisfying auditors. At its most valuable, it is a risk management discipline, one that identifies where exposure is concentrated, quantifies what that exposure costs, and directs remediation resources accordingly.
Risk quantification transforms compliance from a static obligation into a measurable, decision-oriented function.
Platforms like GRACE support this shift, but the underlying change is broader, a move toward continuous, financially grounded, and operationally integrated risk management.
In a regulatory environment growing more demanding and a threat landscape growing more precise, that capability is not a feature.
It is a necessity.
Ready to quantify your compliance risk?
| Explore ComplyX GRACE or book a demo to see risk quantification in action. |
Enjoyed reading this blog? Stay updated with our latest exclusive content by following us on Twitter and LinkedIn.