Discover how attack path mapping and AI-driven pentesting expose hidden risks across hybrid environments and help prevent identity-based cyber-attacks.
Modern enterprises operate across on-premises systems, cloud platforms, and SaaS applications. While this hybrid model drives agility, it also expands the attack surface in ways traditional tools cannot fully monitor. Attackers no longer break in loudly, they move quietly through identities, permissions, and trust relationships. Attack path mapping has emerged as one of the most effective ways to expose these hidden routes before they are exploited.
Executive Summary
Attackers exploit chains of identity relationships, permissions, and trust across hybrid environments. Attack path mapping exposes these hidden connections, showing how a low-privilege access point can lead to critical systems.
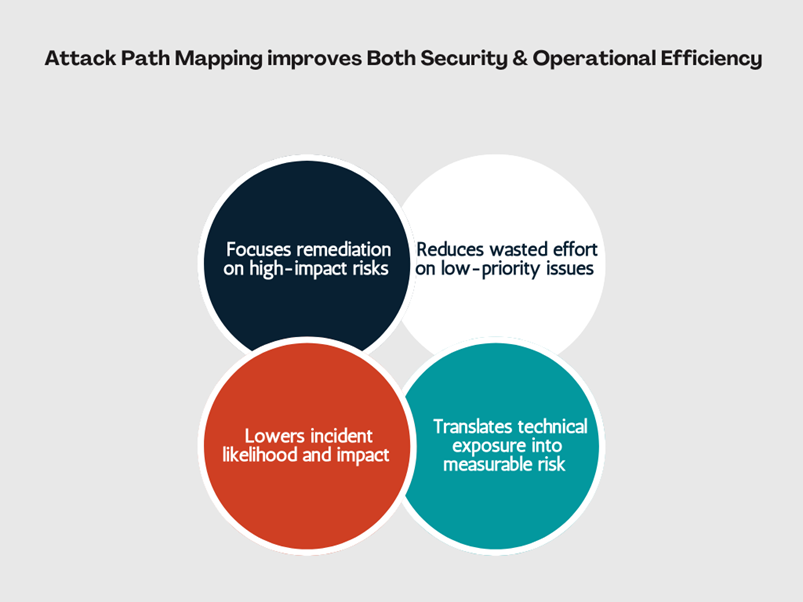
For organizations, this shifts security from reactive detection to proactive risk reduction. Instead of responding to alerts, teams can identify and eliminate high-risk attack paths before they are exploited, supported by automated penetration testing and continuous threat validation.
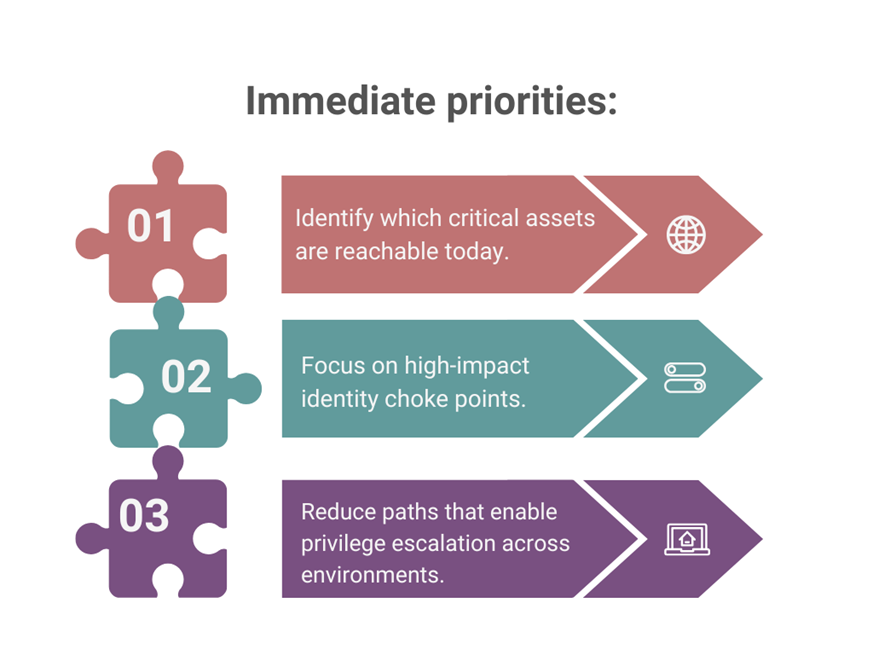
Priorities: What Matters First
For security leaders, the goal is not full visibility, it is risk reduction at speed. Attack path mapping should be treated as a prioritization engine, functioning like a continuous penetration testing program focused on identity risk.
What Is Attack Path Mapping?
Attack path mapping creates a graph-based model connecting users, systems, identities, and permissions. It identifies chains of access that allow a low-privilege account to reach critical assets.
Lateral Movement in Hybrid Environments
Lateral movement, defined by MITRE ATT&CK as tactic TA0008, describes how attackers expand from an initial foothold to high-value targets. In hybrid environments, this often involves identity pivots: from on-premises directories to cloud platforms, across IAM roles, or through SaaS integrations. These movements frequently leave little trace in traditional monitoring tools.
Why Traditional Security Misses It?
Most tools analyze events in isolation. SIEMs rely on correlation rules, EDR lacks visibility into SaaS and serverless systems, and network tools cannot inspect encrypted identity traffic. Unlike traditional penetration testing tools, attack path mapping models identity relationships continuously rather than capturing point-in-time snapshots.
The core issue is structural: they do not model identity relationships and privilege chains, which are the foundation of lateral movement.
The Threat Landscape
Data reinforces this shift:
- CrowdStrike (2024): Breakout time has dropped to 62 minutes, with some attacks occurring in under 2 minutes
- Palo Alto Networks (2024): 80% of cloud exposures involve identity and permissions
- Verizon DBIR (2024): Credential abuse appears in 77% of breaches
- SpecterOps (2023): 94% of AD users have at least one attack path to Domain Admin
How Attack Paths Form in Practice
Consider a typical scenario: a low-privilege user has indirect control over a group, which contains a service account with elevated privileges. That account is synchronized to the cloud and can modify application credentials. Individually, each condition appears harmless, together, they create a path to full compromise. Attack path mapping identifies and prioritizes these chains before attackers exploit them.
The Reality of Remediation Trade-offs
Not all attack paths can be removed without impact. Many exist because they support legitimate operations. In practice, this is often the primary barrier to remediation. Seemingly low-risk permissions are frequently embedded in legacy systems, hardcoded integrations, or business-critical workflows. Removing a single link in an attack path can unintentionally break production processes, trigger outages, or create downstream dependencies that are difficult to trace.
Security teams must balance risk reduction with operational continuity, mitigating or monitoring some paths rather than eliminating them entirely. Effective programs align remediation with business ownership, validate changes in controlled phases, and prioritize high-impact choke points where risk reduction justifies disruption.
Prioritizing Remediation in Complex Environments
Effective remediation focuses on choke points, highly connected identities or roles that enable multiple attack paths. Addressing these nodes can eliminate multiple risks at once. Remediation should also align with business context, using phased changes or compensating controls where disruption is not acceptable.
What a Mature Program Does Differently?
Organizations that succeed with attack path mapping operate with discipline:
- They limit scope early: Start with identity systems and critical assets, not the entire environment.
- They prioritize impact over completeness: Removing one high-value attack path is more effective than analyzing hundreds.
- They align remediation with ownership: Business and application owners are involved early to prevent disruption.
- They integrate into existing workflows: Findings feed directly into Identity Access Management (IAM), PAM, and incident response, not separate dashboards.
Maturity is not defined by visibility; it is defined by consistent risk reduction over time.
Shadow Identities and SaaS Sprawl
A growing share of attack paths originates outside managed environments. Employees adopt SaaS tools, developer platforms, and AI applications without centralized oversight, creating “shadow identities.”
These include personal GitHub accounts, unmanaged OAuth integrations, and third-party connectors. Without accounting for these identities, attack path analysis remains incomplete.
In 2026, this risk is further amplified by AI-native identities. Autonomous agents, MCP-integrated tools, and AI-driven workflows operate with persistent credentials, delegated permissions, and decision-making capabilities, often outside traditional IAM governance. These non-human identities introduce new attack paths through automated actions, tool chaining, and cross-system access, making them difficult to track, constrain, or revoke using conventional controls.
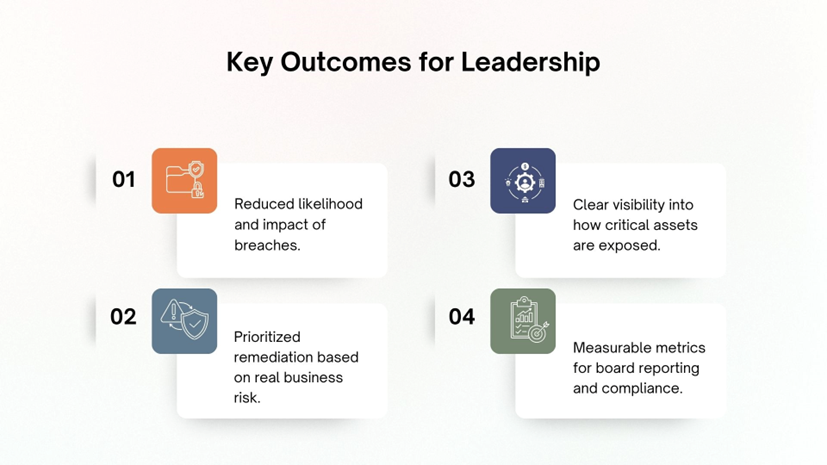
Business and Security Impact
For executives, it provides clear metrics, such as reachable critical assets or eliminated attack paths, enabling better alignment between security investments and business priorities
Attack Path Mapping in Incident Response
During incidents, attack path mapping accelerates response by showing what an attacker can reach from a compromised identity.
Instead of investigating alerts in isolation, teams can immediately identify affected systems and prioritize containment actions. Integrated with response workflows, this reduces mean time to respond (MTTR) and improves the realism of tabletop exercises.
Interpreting Attack Path Metrics
In many environments, critical assets are widely reachable due to accumulated permissions. This should be treated as a high-risk condition. Mature organizations aim to restrict access to controlled, well-monitored paths. The goal is not eliminating all paths but reducing unnecessary ones and continuously validating those that remain.
From a maturity perspective, organizations evolve from basic visibility (identifying paths) to prioritized remediation (eliminating high-risk chains), to continuous validation (ensuring new paths do not emerge unnoticed).
Making Metrics Executive-Ready
For metrics to be meaningful at the leadership level, they must show directional improvement and business impact:
- Reduction in reachable critical assets over time
- Decrease in high-risk identity choke points
- Time taken to eliminate or mitigate critical attack paths
These metrics should be tracked consistently and tied to risk reduction outcomes, not just activity levels.
Operationalizing Attack Path Mapping
Implementation typically starts with identity systems, Active Directory, cloud IAM, and privileged access layers.
A phased approach works best:
- Map relationships (read-only)
- Identify high-risk paths
- Integrate into remediation workflows
Success depends on continuous iteration, not one-time deployment.
Managing Complexity and Cost
Attack path models can generate large volumes of data. Without proper tuning, they risk becoming noisy.

In practice, this introduces a new challenge, what can be described as “alert fatigue 2.0.” Graph-based models often reveal that many identities are indirectly connected to critical assets, creating an overwhelming number of potential attack paths. Without context, this can make everything appear equally urgent.
Effective programs address this by prioritizing choke points, reducing duplicate or overlapping paths, and focusing on paths that materially reduce risk when remediated. Integration with existing workflows.
Aligning with Compliance Frameworks
Attack path mapping also supports frameworks like SOC 2 and ISO/IEC 27001:
- Identifying excessive permissions supports least privilege
- Mapping relationships supports segregation of duties
- Continuous monitoring aligns with ongoing risk assessment
Metrics such as reduced attack paths provide audit evidence, moving beyond static documentation to measurable control effectiveness.
For regulated industries, this also aligns with frameworks such as NIST CSF 2.0, DORA, and NIS2, where continuous risk visibility, identity governance, and resilience are core requirements rather than periodic controls.
Conclusion
Lateral movement defines modern security, with attackers exploiting identity relationships across hybrid environments beyond the reach of traditional tools.
Attack path mapping exposes these hidden chains, enabling organizations to reduce risk before compromise. It is not about mapping everything but consistently eliminating the paths that matter most and balancing risk reduction with business continuity.
So, what are you waiting for? Identify and continuously validate your attack paths with Mirror: AI-driven pentesting, before attackers do.
| Connect with our experts for further discussion! |
Enjoyed reading this blog? Stay updated with our latest exclusive content by following us on Twitter and LinkedIn.












