Cybersecurity has always been a race between attackers and defenders. For years, organizations have relied on penetration testing tools to simulate attacks and uncover vulnerabilities before threat actors do. But in 2026, the rules of this game are changing.
Traditional penetration testing platform are no longer enough on their own. Attack surfaces have expanded, threats have become faster and more intelligent, and security teams are expected to keep up in real time. This is where Mirror, a new AI penetration testing platform, is redefining how organizations approach security testing.
What Is Mirror?
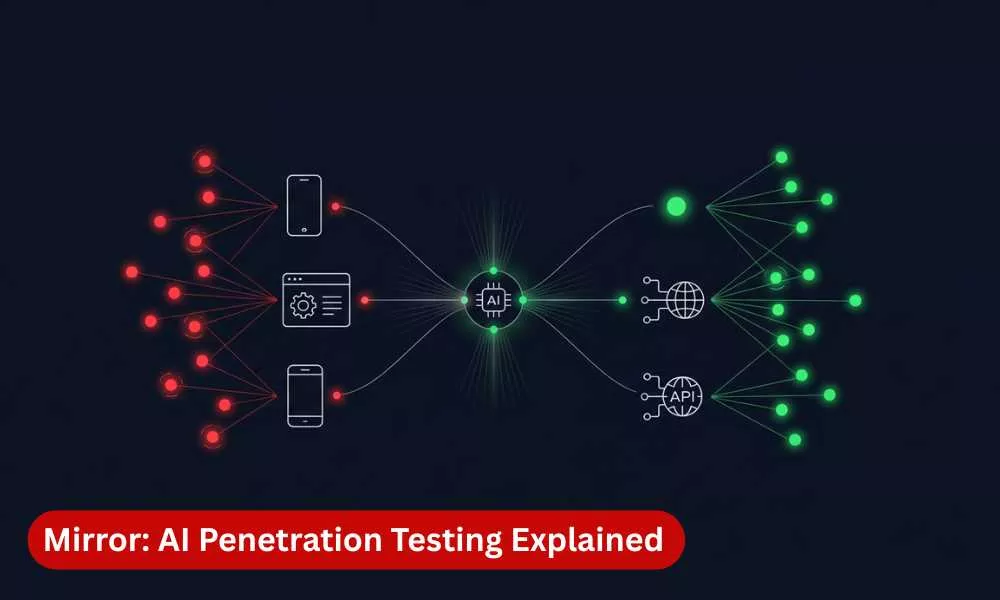
Mirror is an autonomous penetration testing tool designed to simulate real-world cyberattacks across an organization’s entire environment. Unlike traditional tools that operate in silos, Mirror brings together reconnaissance, exploitation, and attack simulation into one intelligent system.
At its core, Mirror uses an agentic AI architecture, meaning it does not just follow predefined scripts. It actively analyzes the environment, identifies potential attack paths, and adapts its approach based on what it discovers.
Instead of running isolated tests, Mirror behaves more like a real attacker. It thinks, pivots, and progresses through multi-stage attack chains, helping organizations understand not just where vulnerabilities exist, but how they can be exploited.
What Does Mirror Do?
Mirror goes beyond traditional vulnerability scanning or manual penetration testing. It performs a full-spectrum security assessment by:
- Discovering assets across networks, cloud environments, APIs, and applications.
- Identifying vulnerabilities in real time.
- Validating whether those vulnerabilities are exploitable.
- Chaining multiple weaknesses into realistic attack paths.
- Simulating lateral movement, privilege escalation, and data exposure scenarios.
This means security teams are not just seeing a list of issues. They are seeing how an attacker could move through their environment step by step.
Mirror also operates continuously, which is critical in modern environments, where infrastructure changes daily. Instead of waiting for the next audit or pentest cycle, organizations get ongoing visibility into their security posture.
How Is Mirror Better Than Traditional Pentest Tools?
Traditional penetration testing relies on skilled practitioners using tools like Nmap, Metasploit, and Burp Suite. These tools remain essential and in the right hands, they’re powerful. But the testing model built around them has limitations:
- Manual and time-intensive
- Point-in-time assessments, typically annual or quarterly
- Constrained by tester availability and hours in the day
- Focused on individual tasks rather than complete attack chains spanning multiple systems
Mirror doesn’t replace the tools. It replaces the model. Automated penetration testing tools like Mirror addresses these gaps in three major ways:
1. Speed and Scale
A comprehensive manual pentest typically takes 2-4 weeks per engagement and covers only one attack surface at a time. Mirror compresses this into hours and tests across six attack surfaces simultaneously: web, API, infrastructure, source code, Android, and iOS.
2. Contextual Intelligence
Traditional scanners detect known vulnerabilities. Mirror understands context. It evaluates whether a vulnerability is exploitable in your specific environment and how it connects to other weaknesses.
3. Continuous Testing
Instead of testing once a quarter or once a year, Mirror runs continuously. It adapts to new deployments, configuration changes, and emerging threats in real time.
The result is not just faster testing, but more accurate and actionable insights.
How Mirror Improves Efficiency for VAPT
Vulnerability Assessment and Penetration Testing (VAPT) has traditionally been resource-heavy. It requires skilled professionals, significant time investment, and coordination across tools.
Mirror enhances VAPT efficiency in several ways:
1. Reduces Manual Effort
By automating repetitive tasks such as asset discovery, scanning, and initial exploitation, Mirror allows security teams to focus on higher-value analysis.
2. Minimizes False Positives
Mirror doesn’t just detect vulnerabilities, it exploits them to confirm they’re real. Every finding comes with proof: the request that triggered it, the response, and reproduction steps. If Mirror can’t exploit it, it doesn’t report it. Security teams spend zero-time triaging false positives because there aren’t any.
3. Accelerates Reporting
Instead of manually compiling reports, Mirror generates structured, compliance-ready outputs aligned with frameworks like MITRE ATT&CK, ISO 27001, and SOC 2.
4. Enables Continuous Validation
VAPT is no longer a one-time activity. Mirror ensures that vulnerabilities are continuously tested, remediations are verified, and new risks are identified as they emerge.
In essence, Mirror transforms VAPT from a periodic exercise into an ongoing security capability.
The Future of VAPT with Mirror
The future of penetration testing is moving toward automation, intelligence, and continuity and Mirror represents this shift significantly.
As organizations adopt cloud-native architectures, APIs, and distributed systems, the attack surface will only grow. At the same time, attackers are increasingly leveraging automation and AI to scale their operations.
To keep up, security teams need tools that can operate at the same speed and intelligence.
Mirror introduces a new model for VAPT:
- From periodic to continuous testing
- From isolated findings to attack narratives
- From manual effort to AI-assisted execution
- From detection to validated exploitation
This does not replace human expertise. Instead, it amplifies it. Security professionals can focus on complex scenarios, strategic decisions, and advanced threat modeling, while Mirror handles large-scale, systematic testing.
The Bottom Line
Penetration testing is no longer just about finding vulnerabilities. It is about understanding how those vulnerabilities can be exploited in real-world scenarios.
Traditional tools still play a critical role and the expertise of skilled pentesters will always matter. But the model of periodic, manual testing cannot keep pace with environments that change every hour. AI-powered platforms like Mirror bring the missing layer: intelligence, speed, and continuity.
The question isn’t whether your team tests. It’s whether your testing keeps up with your deployments.
| Ready to see Mirror in action? Request a demo and experience it firsthand. |
Enjoyed reading this blog? Stay updated with our latest exclusive content by following us on Twitter and LinkedIn.