Organizations must remain vigilant against the relentless threats posed by cybercriminals. Early threat detection is critical, and one essential tool in a security team’s arsenal is Indicators of Compromise (IoCs). Understanding IoCs is fundamental to proactively defending against cyber threats and minimizing damage from cyber incidents.
What are Indicators of Compromise (IoCs)?
Indicators of Compromise (IoCs) are pieces of forensic data that signify potentially malicious activity on a network or system. They serve as digital fingerprints indicating that a security incident, like a breach or malware infection, has occurred or is currently underway. These digital clues help cybersecurity analysts detect and respond swiftly to cyber threats.
Why are IoCs Important in Cybersecurity?
IoCs provide invaluable insight into cyberattacks by identifying evidence of intrusion. They enable organizations to react promptly, limiting damage and disruption to safeguard critical data. By recognizing IoCs early, businesses can strengthen their cyber defenses, reduce response times, and significantly mitigate risks associated with cyber incidents.
Importance of IoCs in Threat Intelligence
Threat intelligence relies heavily on IoCs. They indicate cybersecurity teams about active and emerging threats, enabling analysts to develop proactive defense strategies rather than just reacting after a breach occurs. IoCs help organizations understand attacker behaviors, predict potential breaches, and bolster their overall security posture against future attacks.
How do Indicators of Compromise Work?
Detecting and Analyzing IoCs
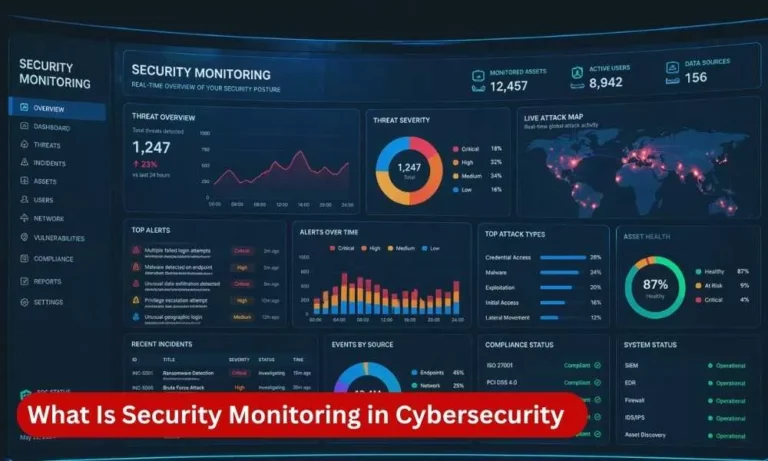
Detecting IoCs involves monitoring your systems for suspicious activity. Security analysts use specialized tools like Intrusion Detection Systems (IDS), Endpoint Detection and Response (EDR), and Security Information and Event Management (SIEM) systems. Through detailed log analysis and correlation of security events, analysts quickly pinpoint threats and initiate appropriate response actions.
IoCs and Cyber Threat Detection
IoCs serve as critical early-warning signals, alerting your team to cyber threats before significant damage occurs. By monitoring for IoCs, security teams can detect cyberattacks at their initial stages, reducing the time attackers spend undetected within systems and networks. This proactive approach minimizes business disruptions and potential data losses.
IoCs in Cybersecurity Frameworks
Within comprehensive cybersecurity frameworks like NIST and ISO 27001, IoCs are integral to incident response and threat hunting strategies. They enable structured identification, response, and documentation processes, making your cybersecurity efforts more organized and effective.
Common Types of Indicators of Compromise
Understanding the various IoC types helps the cybersecurity team stay ahead of threats. Some common types of IoCs your team should look for include the following:
- File Hashes: Unique identifiers linked to malicious software.
- Malicious IP Addresses: Associated with known threat actors.
- Suspicious URLs: Websites known to host malware or phishing content.
- Unusual Network Traffic Patterns: Indicative of data exfiltration or malware communication.
- Registry Key Changes: Unauthorized changes that could signal malware infections.
Indicators of Compromise vs Indicators of Attack
Key Differences Between IoCs and IoAs
While Indicators of Compromise (IoCs) identify evidence of an existing compromise, Indicators of Attack (IoAs) represent behaviors indicative of potential attacks occurring in real-time. IoCs are typically reactive, post-incident indicators, whereas IoAs are proactive indicators, allowing organizations to predict and mitigate threats before a breach occurs.
Why Organizations Need to Understand Both
Effective cybersecurity strategies require leveraging both IoCs and IoAs. IoAs enable proactive threat prevention, while IoCs facilitate rapid response and damage control after compromise detection. Together, they create a robust defense capable of handling sophisticated cyber threats.
Identifying and Responding to IoCs Effectively
How to Identify Indicators of Compromise?
Organizations can identify IoCs through:
- Monitoring network and system activities.
- Reviewing security logs.
- Using threat intelligence tools.
- Employing advanced security detection systems.
Continuous monitoring and skilled cybersecurity analysts are vital in rapidly pinpointing IoCs.
Improving Incident Response with IoCs
Integrating IoCs into incident response plans dramatically improves response efficiency. IoCs provide detailed context for analysts, helping prioritize threats, streamline investigations, and significantly shorten response times, thus minimizing overall incident impact.
How Does Monitoring for IoCs Help Incident Response?
Ongoing IoC monitoring enhances an organization’s ability to recognize and respond to threats quickly. It enables real-time visibility into security incidents, aiding rapid containment and remediation. Regular IoC monitoring empowers security teams to swiftly disrupt attacks and recover from incidents with minimal operational disruption.
Immediate Actions to Handle Identified IoCs
When IoCs are identified, the organization’s initial immediate actions should be:
- Isolate affected systems immediately.
- Collect forensic evidence.
- Notify relevant stakeholders.
- Document the incident thoroughly.
This initial response is critical in limiting further compromise and containing the breach.
Best Practices for Managing IoCs
Effectively managing Indicators of Compromise (IoCs) requires a strategic approach that balances technology, process, and people. Implementing these best practices can help your security team stay ahead of threats and respond swiftly.
Keep Threat Intelligence Database Updated
Regularly refresh your IoC databases with the latest threat information to ensure detection tools recognize new and evolving attack patterns.
Automate Detection and Alerts
Use automation to monitor IoCs continuously and trigger alerts for suspicious activity. This reduces manual workload and speeds up threat identification.
Prioritize Alerts Based on Risk
Assign severity levels and focus on high-risk IoCs first. This helps prevent alert fatigue and ensures critical threats get immediate attention.
Train Security Teams Continuously
Provide ongoing education and hands-on training to keep analysts sharp in identifying and responding to IoCs effectively.
Maintain Clear Documentation
Keep comprehensive and detailed records of IoCs, investigation processes, and incident responses. Proper documentation supports forensic analysis and helps improve future defenses.
Integrate IoC Data Across Tools
Ensure IoC information flows seamlessly between your security platforms for better correlation and faster incident response.
Review and Refine Detection Rules
Regularly evaluate and adjust detection criteria to reduce false positives and improve the accuracy of IoC identification.
By following these best practices, organizations can enhance their threat detection capabilities and build a more resilient cybersecurity posture.
Choosing the Right IoC Monitoring Solution
Selecting the right IoC monitoring tools and solutions involves assessing the organization’s specific needs, existing infrastructure, budget constraints, and desired detection capabilities. Comprehensive evaluation ensures optimal integration and maximum security effectiveness.
Challenges in IoC Management
Managing Indicators of Compromise (IoCs) effectively is not without its hurdles. Security teams often face several common challenges that can hinder timely detection and response. Understanding these challenges helps organizations improve their IoC handling processes.
Alert Fatigue
Security tools can generate a high volume of alerts, many of which may be false positives. Constantly shifting through these alerts can overwhelm analysts, causing significant threats to be overlooked.
False Positives
Not all detected IoCs indicate real threats. False positives waste valuable time and resources investigating benign events, reducing overall security efficiency.
Limited Visibility
Without comprehensive monitoring across all network segments, endpoints, and cloud environments, some IoCs may go unnoticed, allowing attackers to remain hidden.
Resource Constraints
Smaller teams or organizations with limited budgets may struggle to maintain the necessary tools and skilled personnel to monitor and respond to IoCs properly.
Complex Threat Landscape
Attackers constantly change tactics, making it challenging to keep IoC databases updated and detection rules relevant, which can lead to missed detections.
Integration Challenges
IoC data often comes from multiple sources and tools. Lack of seamless integration between systems can slow down correlation and incident response.
Data Overload
Large volumes of IoC data can be difficult to analyze without automation, making it challenging to prioritize which indicators require immediate action.
Addressing these challenges requires a combination of advanced technology, streamlined processes, and ongoing training to help security teams focus on the most critical threats and respond effectively.
Improving Incident Response with Effective IoC Management
Effective IoC management streamlines threat response, reduces attackers’ dwell times, and minimizes cybersecurity risks. Enhancing IoC management practices empowers organizations to sustain robust security measures over time.
Conclusion
Indicators of Compromise are essential for proactive cybersecurity strategies. They help your organization detect threats early, respond effectively, and limit damage.
By leveraging comprehensive IoC practices, advanced monitoring tools, and effective incident response processes, organizations can significantly strengthen their cybersecurity posture and protect business from evolving threats.
| Enhance your cybersecurity approach today by integrating robust IoC practices into your organization’s security framework to stay protected from cyber threats. |
Enjoyed reading this blog? Stay updated with our latest exclusive content by following us on Twitter and LinkedIn.